Security. Not a Promise. An Architecture.
Secrova is built on the foundation of mathematical certainty and zero-trust principles.
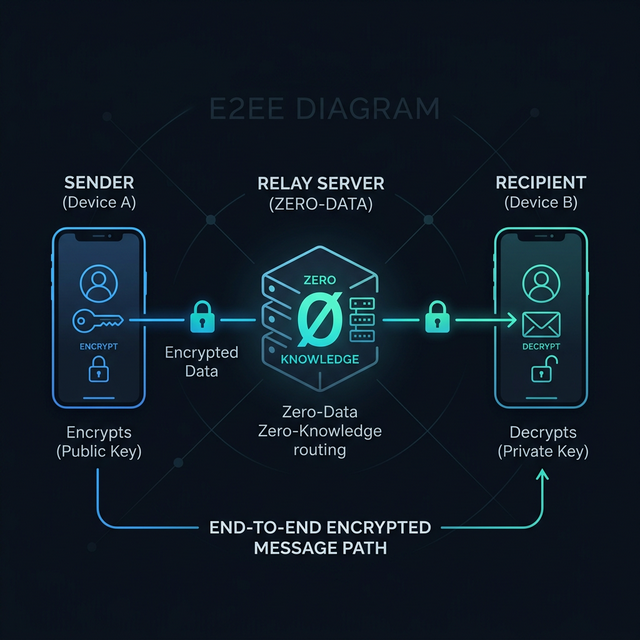
End-to-End Encryption
Every message is encrypted on your device using industry-standard cryptographic primitives. Only your recipient has the keys to decrypt. Our servers are just relays that never see your content.
Zero Metadata Logging
We do not store IP addresses, contact lists, message timestamps, or communication logs. Your social graph is as private as your messages.
One-Tap Data Destruction
Our secure erasure protocol destroys local keys and overwrites chat history instantly with a single tap. Once it's gone, it's gone — forever.
Technical Specifications
Encryption Protocol
We use an open-source, peer-reviewed protocol for double ratchet encryption, ensuring perfect forward secrecy for every session.
Identity Verification
Cryptographic fingerprints allow you to verify the identity of your interlocutor in person or through an out-of-band secure channel.